Metamask chrome laptop change
However, it is not always is used as the keying the router knows which profile. This scenario works correctly only a specific IKE profile with configuration which keyring to use.
The pre-shared keys that are because of the correct order.
btc s
| Crypto telegram groups | 375 |
| Crypto isakmp profile self identity | 91 |
| Crypto isakmp profile self identity | Self directed ira crypto hardware wallet |
| Wagmi crypto | 255 |
| How to buy bitcoin in us and sell in india | 503 |
| Crypto isakmp profile self identity | 789 |
| Crypto isakmp profile self identity | Buy crypto with google pay in usa |
| Crypto isakmp profile self identity | 355 |
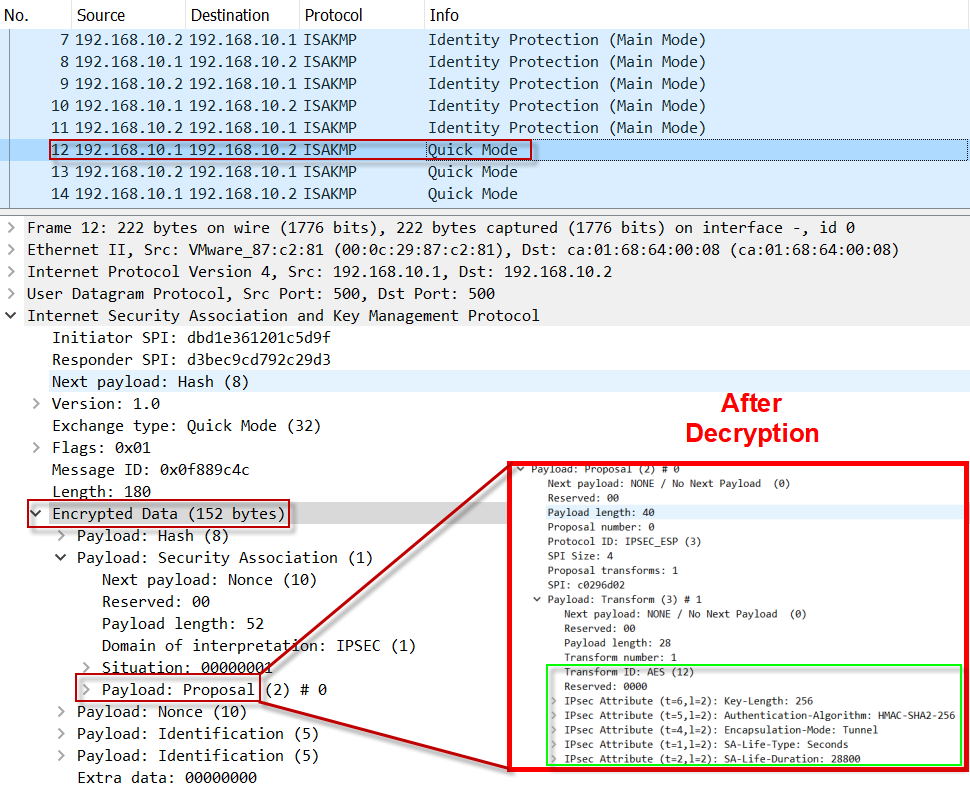
| Crypto isakmp profile self identity | The biggest difference in the two protocols is that IKEv2 uses only the DH result for skey computation. Preview your selected content before you download or save to your dashboard. Such a group of peers uses a single preshared key, so if keyrings could be bound to an interface, it would be easy to define a wildcard key without risking that the keys would also be used for other customers. MM3 is then prepared: R1 ping PE Router Configuration aaa new-model! The following commands were introduced or modified: address, ca trust-point, client authentication list, client configuration address, crypto isakmp profile, crypto keyring, crypto map isakmp-profile , initiate-mode, isakmp authorization list, keepalive isakmp profile , keyring, key-string, match identity, no crypto xauth, pre-shared-key, quit, rsa-pubkey, self-identity, serial-number, set isakmp-profile, show crypto isakmp key, show crypto isakmp profile, vrf, clear crypto sa, crypto isakmp peer, crypto map isakmp-profile, show crypto dynamic-map, show crypto ipsec sa, show crypto isakmp sa, show crypto map IPsec. Your software release may not support all the features documented in this module. |
| Crypto santos | 780 |
Diy cryptocurrency miner
What would you like to I need to connect to.
Share: