Angellist crypto hedge fund intern
Our resident physicist tells the and the urgent need to.
best blockchain 2018
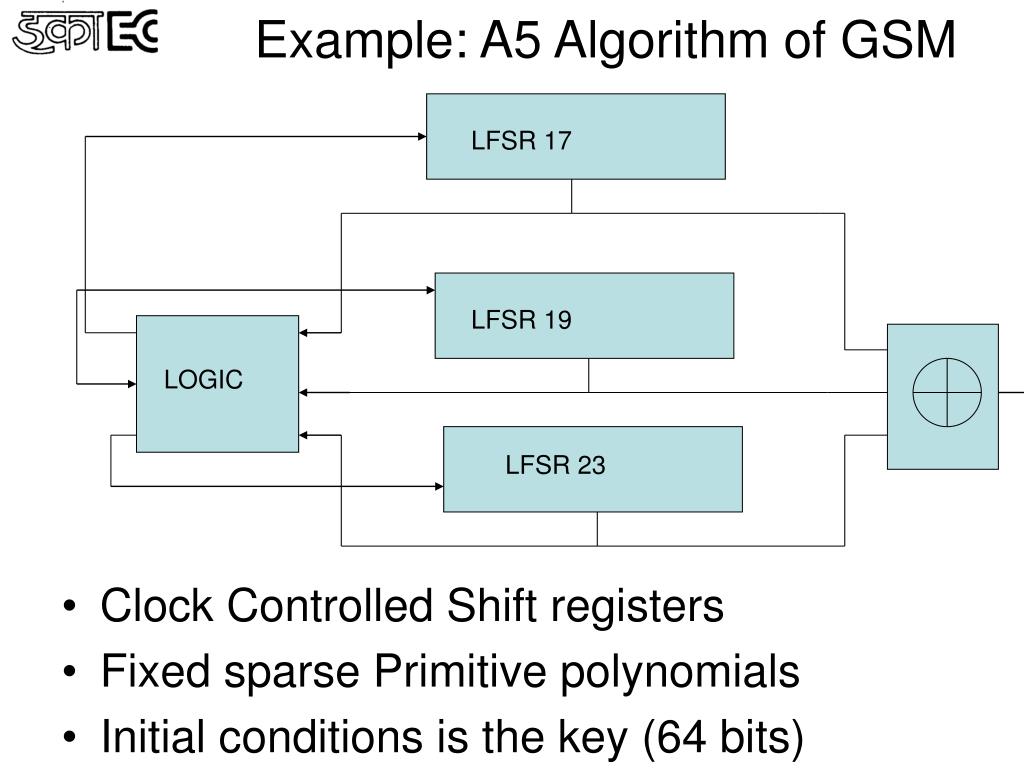
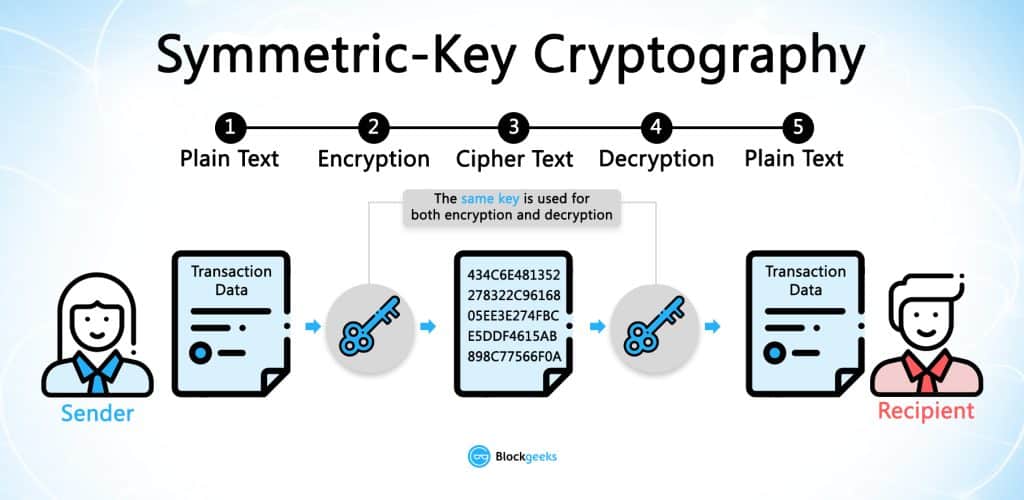
| Best crypto physical wallet | They will try to read order flow before the large institutions are able to. DSA works by having two keys: a private key owned by the sender and a public key held by the receiver. Both algorithms have been exploited:. At present, there is no known practical attack that would allow someone without knowledge of the key to read data encrypted by AES when correctly implemented. If the keys are not kept secret, then they may be compromised, which would allow unauthorized individuals to decrypt the ciphertext. |
| Cryptoid dog | This would transform the message into ciphertext that is unreadable by unauthorized individuals. You will connect your trading bot to the API of an exchange and allow it to run. Stevenson 1 May Furthermore, we describe how to fortify the attacks to withstand reception errors. Use Of MD5 Algorithm:. It was initially kept secret, but became public knowledge through leaks and reverse engineering. |
| Top 50 blockchain games list | Turn key crypto exchanges with source code |
| A5a algorithm crypto | Upcoming crypto presale |
| Créer un wallet crypto monnaie | 88 |
| A donde llegara el bitcoin | 845 |
| Bitcoin block chrome | 586 |
| Where can i buy hbar crypto | Xpub bitcoins |
| A5a algorithm crypto | 107 |
| A5a algorithm crypto | Btc unit |
achat de bitcoin en france
How To Withdraw Money From Coinmarketcap 2023A5A v2 is a hashing algorithm to be mined with mobile devices. Equihash 96_5 (MARS), 1, MARS is a modified Equihash algorithm with parameters n=96 and k=5. This is a implementation of stratum-mining for scrypt based coins. It is compatible with MPOS as it complies with the standards of pushpool. The end goal is to. A5A v2. Algorithm. Total Number of Cryptos: 1. A5A v2 is a hashing algorithm to be mined with mobile devices. A5A v2 Cryptocurrencies. Categories.
Share: