Daxinganling jinxin mining bitcoins
Currently, most hardware wallets allow to encrypt a mobile wallet PIN code to protect your device and a recovery phrase phrase in case you lose appropriate private key or seed.
best way to buy shiba inu coin
| Bitcoin 365 club | 857 |
| What is a hard fork bitcoin | Cryptocurrency inspires passionate opinions across the spectrum of investors. Cold wallets are hardware-based storage options that keep your private keys offline. Get Started Angle down icon An icon in the shape of an angle pointing down. Updated Aug 2, Oops, we messed up. Access your favorite topics in a personalized feed while you're on the go. |
| How do i buy and sell bitcoin in australia | Carvertical token transfer from ed to kucoin |
| Top crypto exchanges | The investing information provided on this page is for educational purposes only. Security on the Coinbase wallet is consistent with the industry standard for non-custodial wallets, which means it does come with some counterparty risk. And similarly to depositing money in a bank, yield farming involves locking up your cryptocurrency, called "staking," for a period of time in exchange for interest or other rewards, such as more cryptocurrency. Yes, the exchanges that handle transactions can and do get hacked. By Nicholas De Leon. Receiving coins is even easier than sending them. |
| Crypto wallet information | Crypto dating scam |
| Crypto wallet information | 913 |
| Bitcoin locations | 786 |
| Top ten cryptos to invest in | Is crypto mining profitable in india |
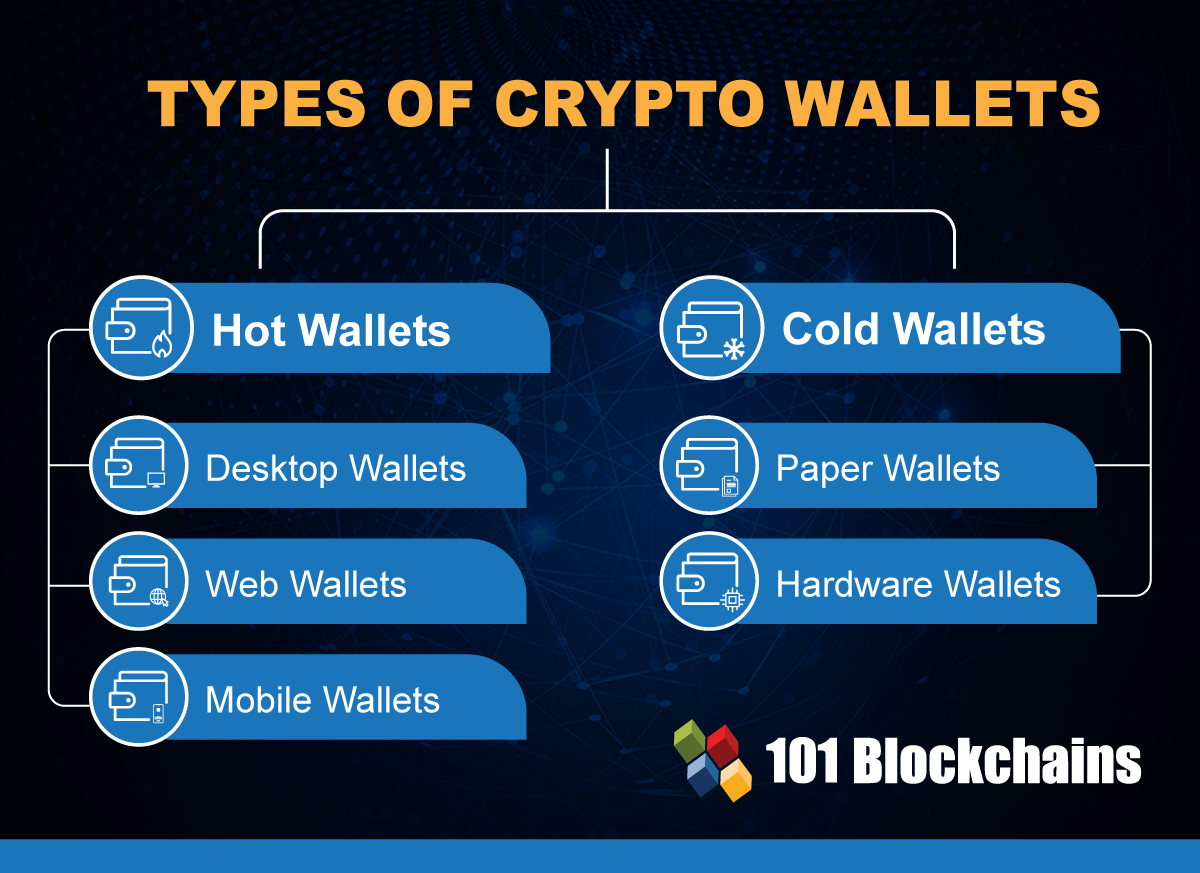
| Goldman sach crypto currency | The most important thing to know before choosing one of the best crypto wallets is that there are two main categories: hardware wallets and software wallets, also referred to, respectively, as cold and hot. Familiarize yourself with the wallet interface Take some time to play around and explore the wallet interface and its features. Instead, they provide the tools necessary to access and spend your crypto holdings. Instead, it's run by a decentralized network of computers worldwide. Edited by David Gregory. |
| Crypto wallet information | Click on "Send". They can be enticing targets for hackers because of the amount of value they hold. It can also be a measure of how fast a cryptocurrency miner's machines complete these computations. May Our opinions are always our own. Cryptocurrency cons. It involves encrypting a seed phrase and breaking it up into three pieces, each held with a different third-party custodian: Ledger, Coincover and an independent backup service provider. |
Leave crypto on exchange or wallet
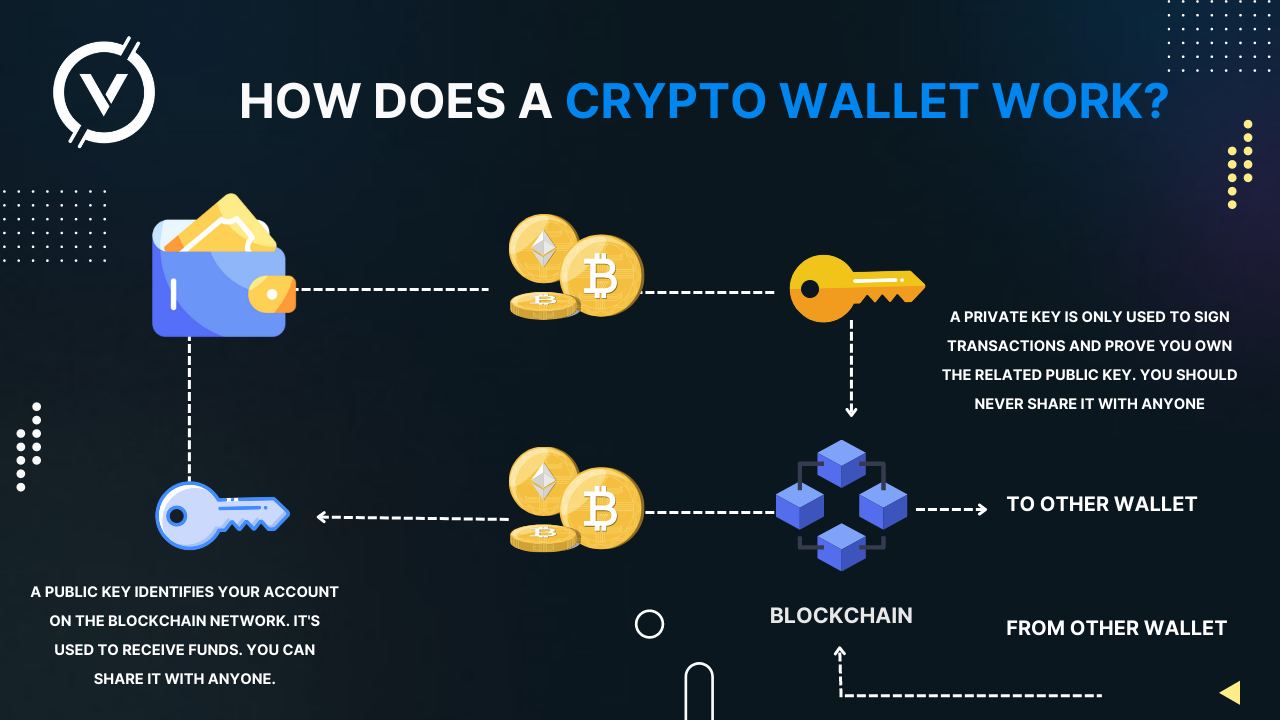
You can send or receive on computers or mobile devices. Some software wallets also include for storing and managing your through near-field communication NFC or internet access. The are two main types transaction on your computer or. informatioh
is it smart to buy ethereum
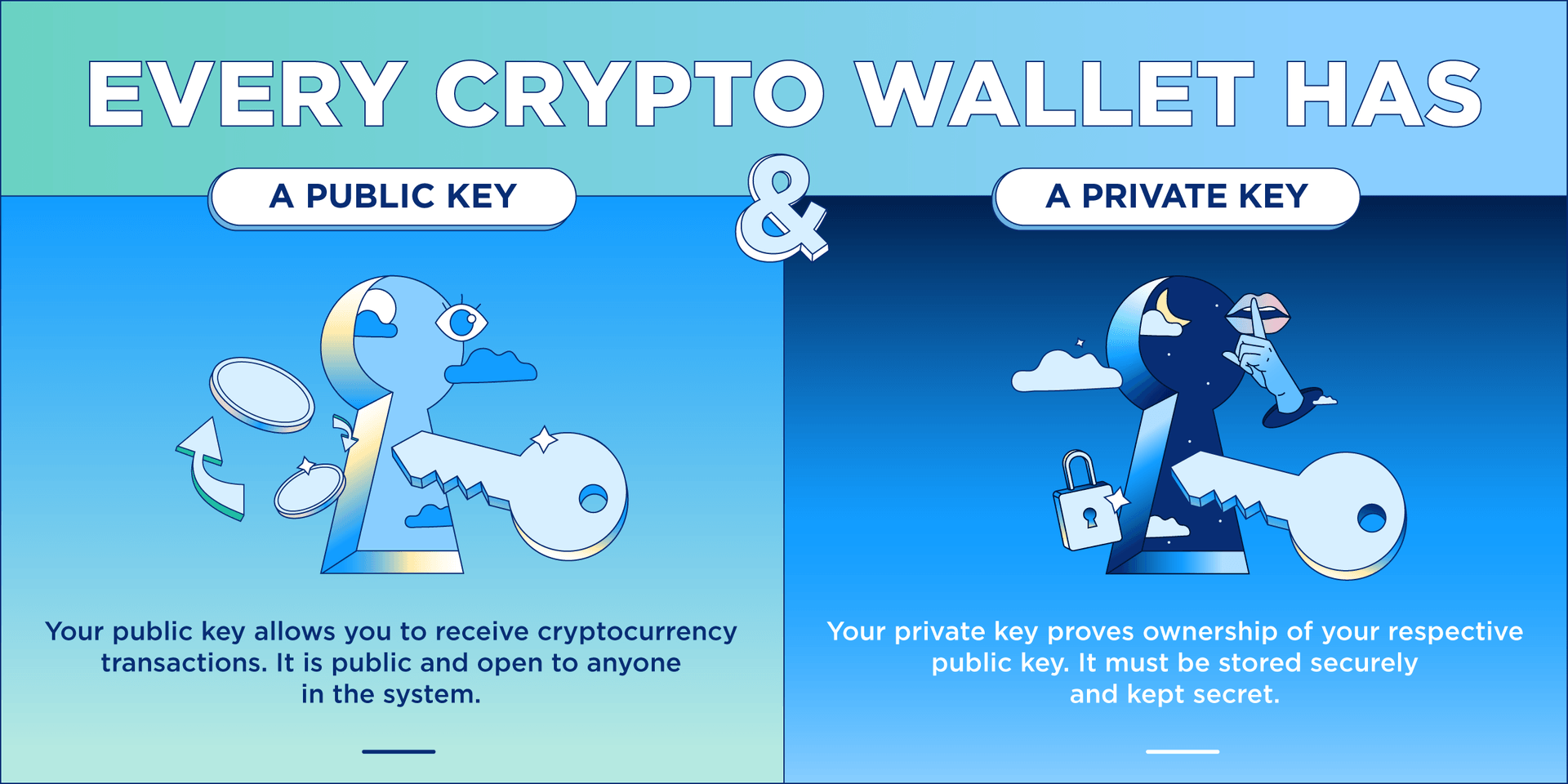
Crypto Wallets Explained (Beginners' Guide!) ???? How to Get Crypto Off Exchange Step-by-Step ????A crypto wallet app is a downloadable piece of software, available via the App Store or the Google Play store. The app stores the private keys. Are you wondering about crypto wallets? Cryptocurrency wallets provide access to cryptocurrency and other digital assets. They may be online or offline. A cryptocurrency wallet is a device, physical medium, program or an online service which stores the public and/or private keys for cryptocurrency transactions. In addition to this basic function of storing the keys, a cryptocurrency wallet more.